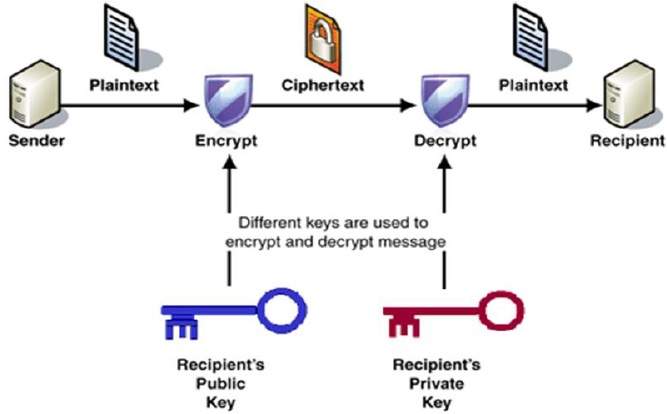
PKC utilizes two different types of encryption algorithms: symmetric and asymmetric algorithms. Symmetric algorithms use the same key for encrypting and decrypting data, while asymmetric algorithms use a pair of keys – one public key for encrypting and one private key for decrypting. Keyfactor Code Assure is a Public Key Cryptography (PKC) system that uses an encryption algorithm to protect the confidentiality and integrity of data. In this article, we will discuss how each type of algorithm works to ensure secure communication between two entities.
RSA Encryption Algorithm
The RSA encryption algorithm is one of the most well-known encryption algorithms in public key cryptography. It was invented in 1977 by Ron Rivest, Adi Shamir, and Leonard Adleman and is named after their surnames. This encryption algorithm is based on asymmetric encryption, where two different keys are generated for encrypting and decrypting data.
The public key can be shared with anyone, while the private key is kept secret. The RSA algorithm is widely used for secure online transactions, email encryption, and digital signatures.
Elliptic Curve Cryptography (ECC)
Elliptic Curve Cryptography (ECC) is a public key encryption algorithm that uses elliptic curves to generate public and private keys. The algorithm is based on mathematical functions that are difficult to break, even with sophisticated brute-force methods.
ECC is known for its speed and low power consumption, making it ideal for mobile devices and other resources with limited processing power. ECC is widely used in secure communications, including web browsing, messaging apps, and email encryption.
Diffie-Hellman Key Exchange
The Diffie-Hellman key exchange is another popular encryption algorithm used in PKC. This algorithm was first proposed by Whitfield Diffie and Martin Hellman in 1976. It is based on a process that allows two parties to establish a shared secret key over an unsecured communication channel.
The Diffie-Hellman key exchange is typically a building block for other encryption algorithms. For example, it can be combined with the RSA algorithm to provide an extra layer of security.
Advanced Encryption Standard (AES)
The Advanced Encryption Standard (AES) is a widely used symmetric encryption algorithm selected as the new encryption standard by the U.S. government in 2001. This algorithm uses a block cipher system, where data is encrypted in fixed-size blocks. AES is known for its speed and security, and it is used to protect sensitive data in various applications, including online banking, cloud storage, and e-commerce transactions.
Blowfish Encryption Algorithm
The Blowfish encryption algorithm is another popular symmetric encryption algorithm designed by Bruce Schneier in 1993. This algorithm uses a variable length key, making it suitable for securing data of different sizes. Blowfish is known for its speed and flexibility, and it is widely used for data encryption in various applications, including password storage, file encryption, and VPN (virtual private network) connections.
Digital Signature Algorithm (DSA)
This algorithm is used to verify the authenticity of digital messages or documents. A digital signature is a mathematical function attached to a message or document to prove it has not been tampered with. DSA encryption is used to sign digital certificates, SSL/TLS connections, and other digital documents.
Additionally, DSA is also used for authentication and non-repudiation. This makes it an essential tool for establishing trust between two entities.
Conclusion
In conclusion, encryption algorithms are an essential part of modern-day communication and play a critical role in keeping our data secure. The different types of encryption algorithms used in PKC are designed to provide different levels of security and efficiency, depending on the specific requirements of each application. As technology continues to evolve, so do encryption algorithms. Developers and users must stay up-to-date with the latest encryption technologies and best practices to protect their data.